
Dr. Antje Winkler
Offensive Security
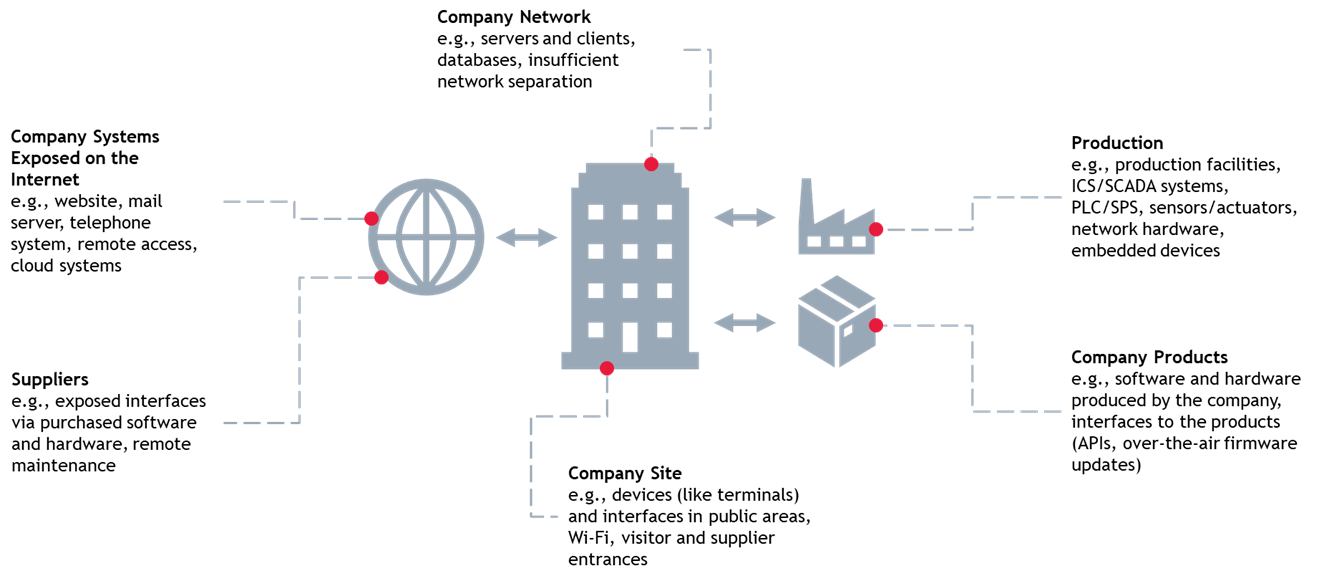
Increasing digitization, networking, and outsourcing of digital infrastructures - to cloud providers, for example - are opening new ways for attackers to infiltrate companies. Whether through systems exposed on the internet, insufficient access controls at the company site, or seemingly trustworthy communication channels with suppliers and partners, there are numerous attack vectors which must be considered:
As BDO Cyber Security GmbH, we help you identify relevant threats, recognize vulnerabilities and define appropriate measures. With our experience, we support you as a strong partner in all matters related to cyber security.




Our experienced team of penetration testers and Red Team professionals holds various certifications, including:
In dedicated hacking sessions, our team analyzes various commercially available hardware and software products. Discovered vulnerabilities are published as CVEs. You can find the corresponding overview here: Advisories.
To provide you with comprehensive analyses of various IoT and embedded devices, we operate a state-of-the-art hardware testing laboratory. Our lab equipment enables the examination of your devices across multiple layers, ensuring precise and reliable outcomes.
Our specialized radio testing environment features a shielding unit for isolating radio technologies, e.g., TCUs and LTE modules. This effectively avoids interferences and sources of disturbance. Using tools like software-defined radios, we analyze various wireless technologies, including 2G, 4G (LTE), 5G, LoRaWAN, ZigBee, Wi-Fi, NFC, RFID, and Bluetooth. For the analysis of mobile communication (e.g. 2G, 4G, 5G), we have a test network with our own base station. This enables us to monitor communication channels and analyze data transmission in detail. Additionally, the radio testing environment allows for interception and manipulation attempts of over-the-air firmware updates.
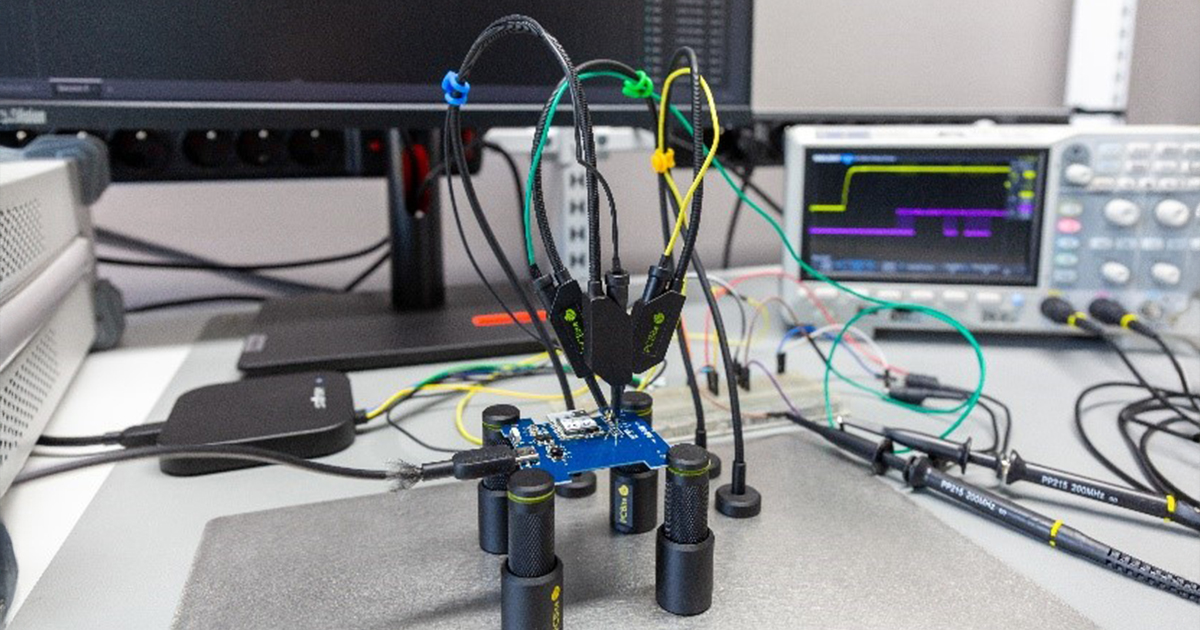
In addition to the radio testing environment, our laboratory is equipped with a hardware testing station. This station is designed to examine various device types in their intact state or to conduct targeted manipulation attempts through hardware modifications. Equipped with a digital oscilloscope and logic analyzers, we can precisely analyze data transmission over physical interfaces such as USB, UART, SPI, or JTAG. For non-invasive tests, we use PCB holders and test probes. Upon request, we also perform more invasive manipulation and extraction attempts, for example, to access internal data in memory modules.
What should you consider? What key factors should you address? We are here to support you with these and any other concerns.